Malware and web-based cyber-attacks are the most popular forms of cyber-attacks. Unfortunately, these attacks are growing in their complexity and methods of delivery.
4,000 ransomware attacks occurred per day in 2016 (How to Protect Your Networks from Ransomware). This number has increased exponentially since then and is expected to continue to grow in future years.
Malware includes viruses, worms, trojans, ransomware, spyware, adware, etc. and is primarily installed via phishing schemes. A phishing attack is when employees click rogue links or open malicious attachments, they unknowingly give hackers remote access to infect their systems.
Looking to stop phishing attacks? Learn about our employee education and mock phishing attack campaign. http://www.raymorgan.com/stop-phishing/
One wrong move and sensitive company data or personally identifiable information, such as your social security number, could become encrypted and/or stolen.
Ransomware is the malware of choice now. You may have heard of CryptoLocker, CryptoWall and now Locky, malicious software that locks you out of your files and demands ransom payment for recovery. Factoring in this ongoing trend, cybercrime is becoming increasingly costly.
Did You Know?
79 percent of small to medium sized businesses (SMBs) don’t have an incident response plan.
Signature-based antivirus solutions detect on average less than 19 percent of malware threats.
Ransomware is becoming more expensive, with the average ransom averaging around $679.
The annual cost of global cybercrime damages is estimated to cost $6 trillion by 2021.
51 percent of business owners are unfamiliar with unified threat management (UTM) and do not fully understand its security benefits.
Multi-Layered Threat Protection and Prevention
Businesses don’t always have the time, bandwidth or resources to stay up-to-date on the latest security processes. The easiest and most beneficial solution for most SMBs is to partner with an MSP (replace with a Managed IT Provider) like Ray Morgan Company.Together, we can minimize your business’ risk and develop a plan that focuses on resiliency, not only prevention. IT security best practices call for a multi-layered approach, and we can provide that for you.
Changes in Cyber-Security Maintenance
Due to the time-consuming nature of data security the IT industry is seeing a trend in outsourced network monitoring. An outsourced model ensures that business can focus on activities related to their industry. By outsourcing cybersecurity maintenance business owners and Chief Information Officers (CIOs) are able to open up bandwidth for them and their team to focus on internal technology goals and initiatives.
Commonly outsourced cybersecurity tasks include:
- Reviewing firewall rules
- Updating your firewall
- Patching the latest vulnerabilities discovered
- Maintaining required controls and standard certifications, such as: ISO, SSAE16, HIPAA, SOX, etc.
- Filtering web content
- Updating software
Your Ultimate Failsafe
Ray Morgan Company can be the expert you can turn to in case of a ransomware or other cyber-attack. As your Manage IT Provider, Ray Morgan Company helps businesses take steps take to minimize interruption to your business and profitability. When you work with Ray Morgan Company, you can rest easy knowing that your network is secure, your data is protected and that we’re available 24x7x365 for any and all of your support needs.
Information Security:
Businesses Need IT, We Can Provide IT
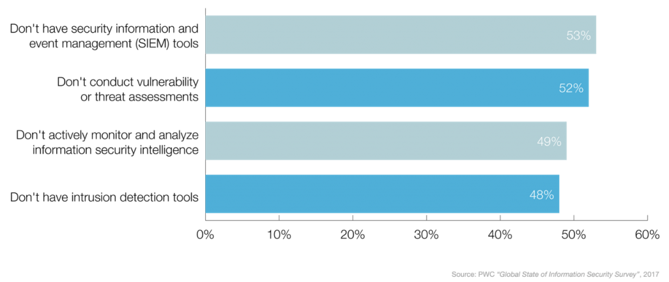
Due to the quickly evolving cybersecurity landscape, many small & medium businesses lack the ability to keep up and are ill-prepared for the threats that exist today. Below are the percentage of organizations that don’t have the following threat detection tools and processes in place.
Small & medium sized businesses can look to partner with Ray Morgan Company to bridge this skills gap and gain access to the expertise needed to stay protected. We are here to support your business 24x7x365 to ensure that no matter what type of threat enters your network, we can help keep your business secure.
Contact us today for more information! Fill out the form below: